Vitrium Security has different encryptions, includes secured PDF file and secured web document, to protect valuable and confidential documents.
Read more like this
Things to consider: document security systems and the way we access and distribute documents continue to evolve, moving towards efficiency and convenience.
Protect and control your PDF documents and PDF content without having to install software, plug-ins or readers. Protectedpdf creates reader-friendly protected PDF documents.
How much would document leaks cost your organization? Discover why you need to protect your documents with Vitrium Security.
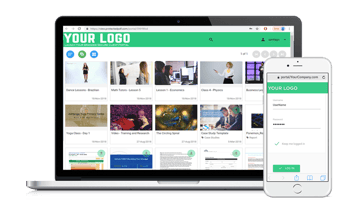
Create your branded Secure Client Portal with Vitrium Security. Offer your audience a secure place to access all videos, documents, and images associated with their credentials.